11 Easy ways to protect your online privacy in 2025
NEWNow you can listen to News articles!
Privacy is more difficult to protect in a world where everything is connected.
Whether you are chatting with an AI, checking your email or using your smartphone, your personal information is collected, tracked and sometimes it is sold.
But protecting your privacy in 2025 does not have to be overwhelming. With some practical steps, you can regain control of your data and make your life online safer. This guide guides it through 11 easy to start.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my free -fashionable scam survival guide when you join.

Scrabble pieces form the word “scam.” (Kurt “Cyberguy” Knutsson)
1. It is not estimated: even with ia tools like chatgpt
Chatbots of AI as chatgpt are useful, but they are not private magazines. The owners of the platform may have privacy policies and use the latest security measures, but that does not mean that the guard should lower. When using these tools, refrain from sharing any personal information, such as your name, address, date of birth, passwords, financial details or confidential conversations. Remember that IA systems store and process their entries, and despite security promises, data violations may occur.
Stofkers can exploit their data from only 1 chatgpt search
Advice: Try all online forms of interaction of AI as public forums. Keep your generic examples and use caution with anything that can identify it.
If you are going to enter your personal information while using these AI tools, make sure there is an option to prevent it from sharing. In chatgpt, for example, do the following:
- Gonna Settings.
- Click Data Controls.
- Tap Improve the model for all.
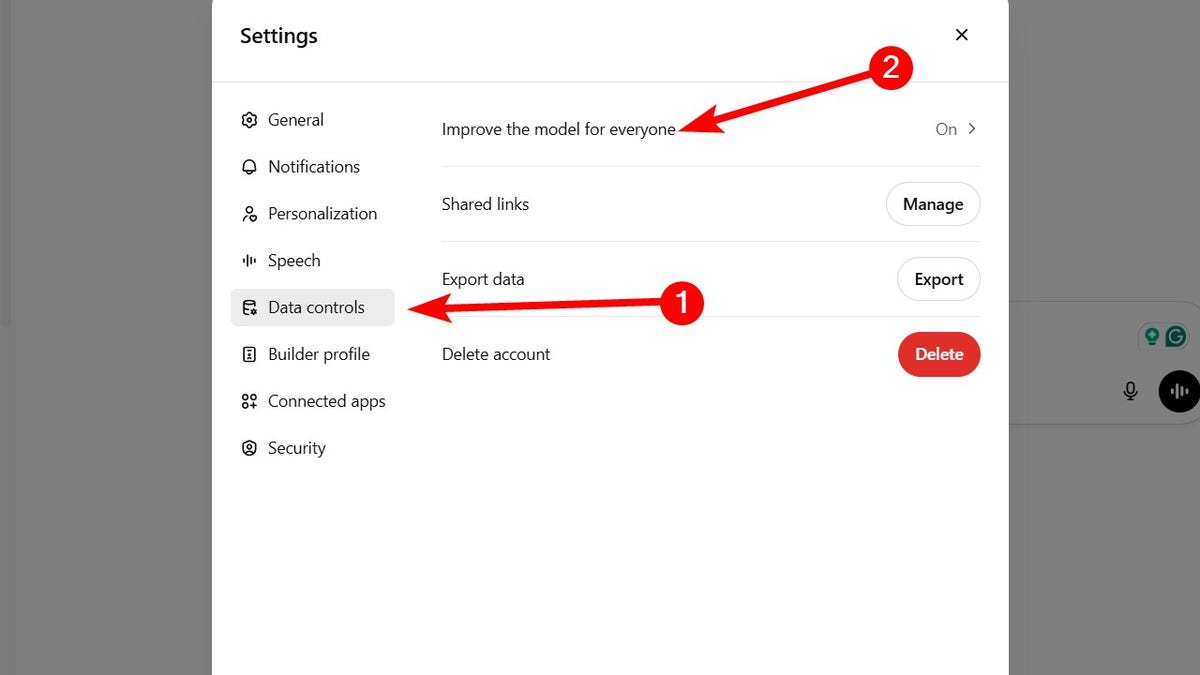
Steps to prevent Chatgpt from sharing your personal information (Kurt “Cyberguy” Knutsson)
- Alternate Improve the model for all.
- Click Made.
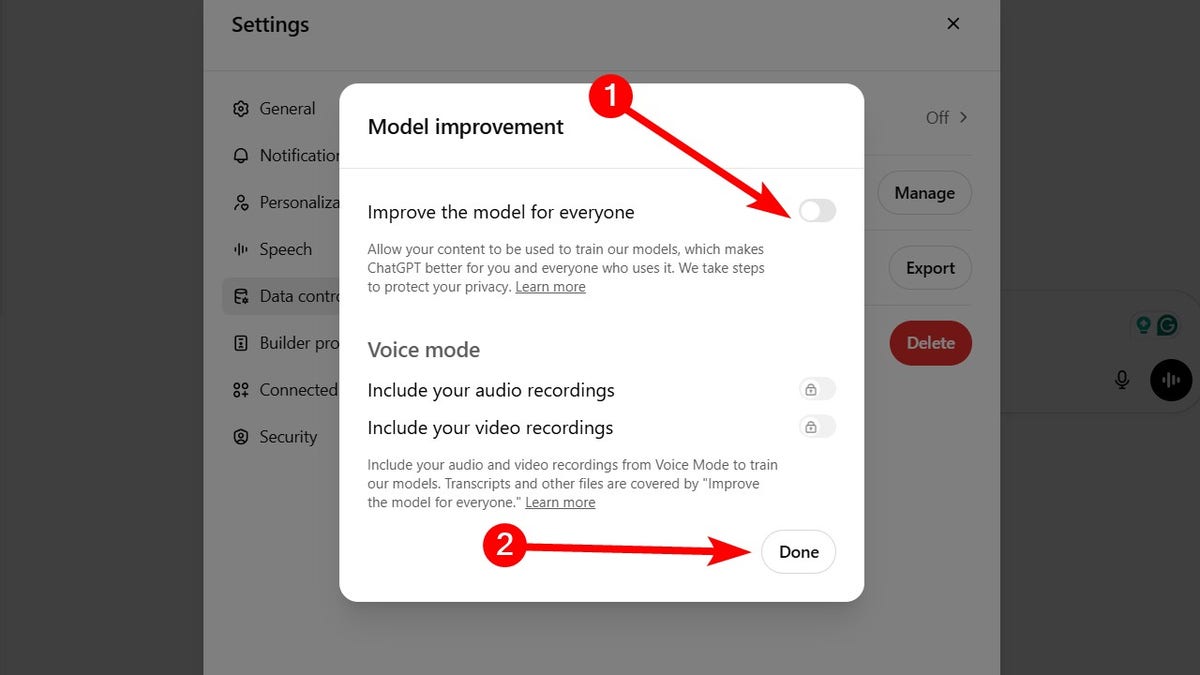
Steps to prevent Chatgpt from sharing your personal information (Kurt “Cyberguy” Knutsson)
Why does it matter: IA tools may seem personal, but they are not safe vaults. The protection of what it shares helps prevent misuse, identity theft or violation data leaks.
Clean your phone: speed, storage and increase in privacy in minutes
2. Use alias email addresses
Your email is often the key to your identity online and a common goal for spam. By creating disposable alias of email that forward the messages to their main entrance tray, you can maintain your real hidden address of websites and services. These unique alias act as shields, so if one begins to be spam or is involved in a data violation, it can simply deactivate it without affecting its main email account.
My main recommendation to avoid being flooded with spam emails is To use an e -mail address from alias. An Alias email address is an additional email address that can be used to receive emails in the same mailbox as the main email address. It acts as a forwarding address, directing the emails to the main email address.
In addition to creating disposable email accounts for online records and other circumstances in which you do not want to reveal your main email address, alias email addresses are useful to handle and organize incoming communications.
Sometimes, it is better to create several email alias so you don’t have to worry about getting tons of unwanted mail or taking your information in data violation. An alias email address is an excellent way to stop receiving a constant spam mail simply by eliminating the email address. See my review of the best safe and private email services here.
Why does it matter: You remain in anonymity, avoid data leaks and you never have to change your main email address again.
The best antivirus for Mac, PC, iPhones and Androids – Cyberguys Picks
3. Take advantage of Facebook’s privacy check -up
Meta frequently updates its privacy settings, so it is better to regularly verify to see how you can improve your privacy. Use Facebook’s Privacy check Tool to review and adjust the crucial configuration, including subsequent visibility, application permits, search visibility and friends application configuration. This comprehensive tool helps guarantee that your profile remains as private as you want. You can find the tool following these steps:
- Log in your Facebook application On your phone.
- Then click on the Menu icon In the lower right.
- Tap Settings.
- Click Privacy check.
Once you open the privacy check, it will be guided through several key areas to customize your privacy preferences and better control your information.
- Who can see what you share? Adjust who can see your publications, photos and profile details to limit access to only people you trust.
- How people can meet you on Facebook: Administer who can send your friendship requests, find it using your email or phone number, and decide if your profile appears in the search engines.
- Your data setting on Facebook: Check what applications and websites they have access to your Facebook data and delete anyone who does not use or trust.
- How to keep your account safe: Configure the authentication of two factors, update your password and monitor login alerts to protect your unauthorized access account.
- Your advertising preferences on Facebook: Control how Facebook uses your activity to show personalized ads and choose not to participate in categories that feel too intrusive.
Fast advice: Establish a reminder to run a privacy check every few months, especially after the main Facebook updates. In this way, you will always have control of your information.
Why does it matter: The social media platforms thrive in their personal data. Adjusting its configuration regularly puts it in control of what others and Facebook can see and use.
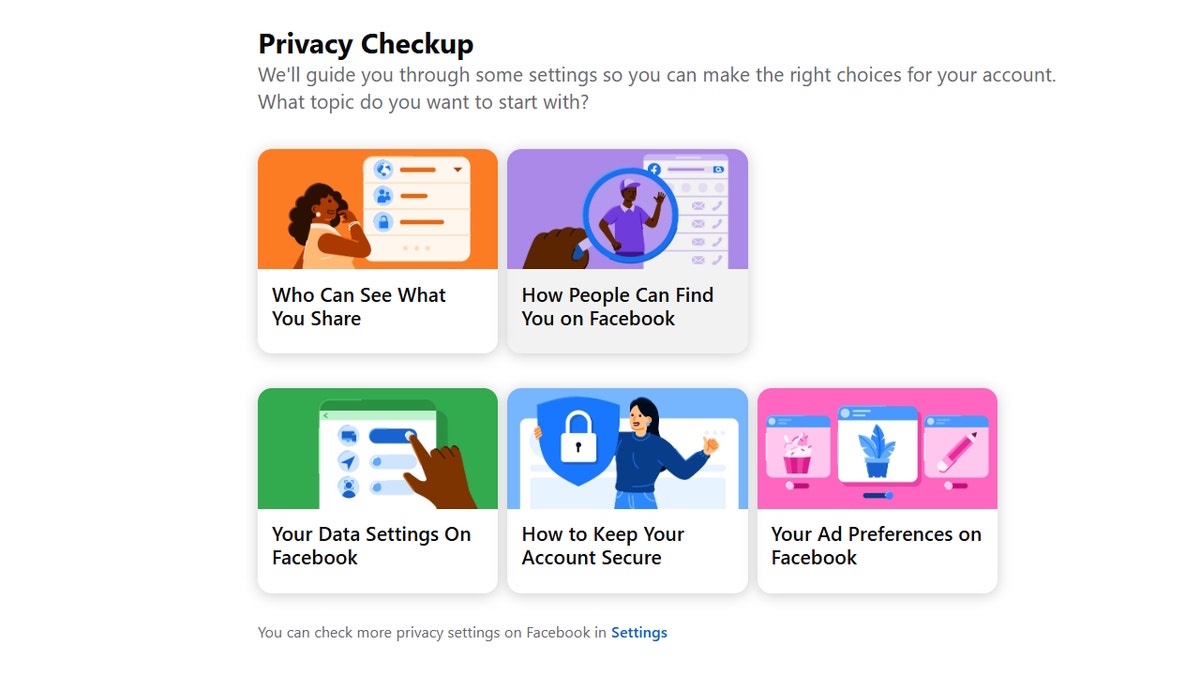
Facebook privacy review (Kurt “Cyberguy” Knutsson)
How to protect your privacy and online safety in your next cruise vacations
4. Automatically scrubbing
Its name, telephone number and house address can already appear in people search sites such as Spokeo, Whitepages and Besverified. These data corridors collect and sell their personal information without even knowing it. Fortunately, personal data removal services are available to protect your privacy. They automatically send legal elimination requests to hundreds of data corridors. They also go further by monitoring them continuously in case these third parties get their information again.
While no service can guarantee the complete elimination of your Internet data, a data removal service is really an intelligent option. They are not cheap and it is not your privacy. These services do all the work by you by actively monitoring and systematically erasing your personal information from hundreds of websites. It is what gives me peace of mind and has proven to be the most effective way to erase your personal internet data. By limiting the available information, it reduces the risk of cross -references data of infractions with information they can find in the dark network, which makes it difficult to be pointed out. See my best selections to obtain data removal services here.
Get a free scan To find out if your personal information is now available on the web.
Why does it matter: How much less personal information about you online, the more difficult it is for scams and identity thieves to aim you and the tranquility more you will have.
10 simple steps to improve the safety and privacy of your smartphone
5. Use a privacy -centered messaging application
If you are still using standard text messages or platforms such as Facebook Messenger, it is time to update to a safer option. Applications like Signal and session Offer an end -to -end encryption, without advertisements and without metadata monitoring, which means that they cannot see who is talking or what they are saying. Both applications admit messages of disappearance, which gives you more control over how long your conversations stay.
Why does it matter: Their messages remain private and cannot be accessed by computer pirates, advertisers or the application developers themselves.
6. Let Google track each movement
Google collects a large amount of data from its searches, YouTube views, Gmail activity and location history, all of which feed the directed advertising. You can stop much of this follow -up by turning off the customization of AD and eliminating your activities history. This is what you should do:
- Go to Google’s My advertising center.
- Find the Advertisement customization section.
- Alternate the switch to turn off advertisement customization. This prevents Google from using your activity to adapt the ads.
Manage the history history
- In My advertising center or through your Google account, go to Data and privacy.
- Low History configurationreview and pause or delete: Web and Application Activity, YouTube story and HISTORY OF THE LOCATION (if applicable).
Eliminate existing activity data
- Select Manage all web and application activity, Manage the entire YouTube storyetc.
- Eliminate past activity choosing A time range (for example, “all time”) and Confirming the elimination For each category.
Choose not to be of third -party advertising customization
- Move to Ads configuration and look for third -party advertisement options.
- Opt outside the advertising customization of partner sites If available.
- If you have several Google accounts, Repeat these steps For each account.
Why does it matter: Advertisement monitoring reduces how much your online behavior is used to build a profile in you, often without your knowledge.
7. Disable the location tracking on your smartphone
Applications They do not need to know each movement. Disable or limit location monitoring is one of the simplest ways to protect your physical privacy. This is what you should do:
iPhone:
- Gonna Settings.
- Tap Privacy and safety.
- Click Location services.
- Show down and touch the application you want to manage.
- Choose your favorite configuration: Never To block the access completely; Ask next time or when I share To allow location only with your permission; While using the application To allow location only when the application is open.
For applications such as maps, alternate Precise location outside to avoid precise monitoring.
To disable the monitoring of the location completely, altere Location services Off at the top of the location services page (this will prevent all applications from using their location).
Android:
SEthings can vary according to the manufacturer of your Android phone.
- Gonna Settings.
- Touch location.
- Tap Application permits either Application location permits.
- You will see a list of applications grouped by its location access: allowed all the time; Allowed only while used; Ask every time; Not allowed.
- Tap any application To change your location permit. Choose between: Allow all the time; Allow only while using the application; Ask every time; No permission.
For applications that have access to location, you can also turn Precise location igniting or off if you want to limit precision. Repeat for each application you want to manage.
Advice: If you want to prevent all applications from accessing your location, it can Disable the location At the top of the location configuration page.
Why does it matter: It prevents applications, advertisers and even their operating system from creating a detailed map of their daily routines.
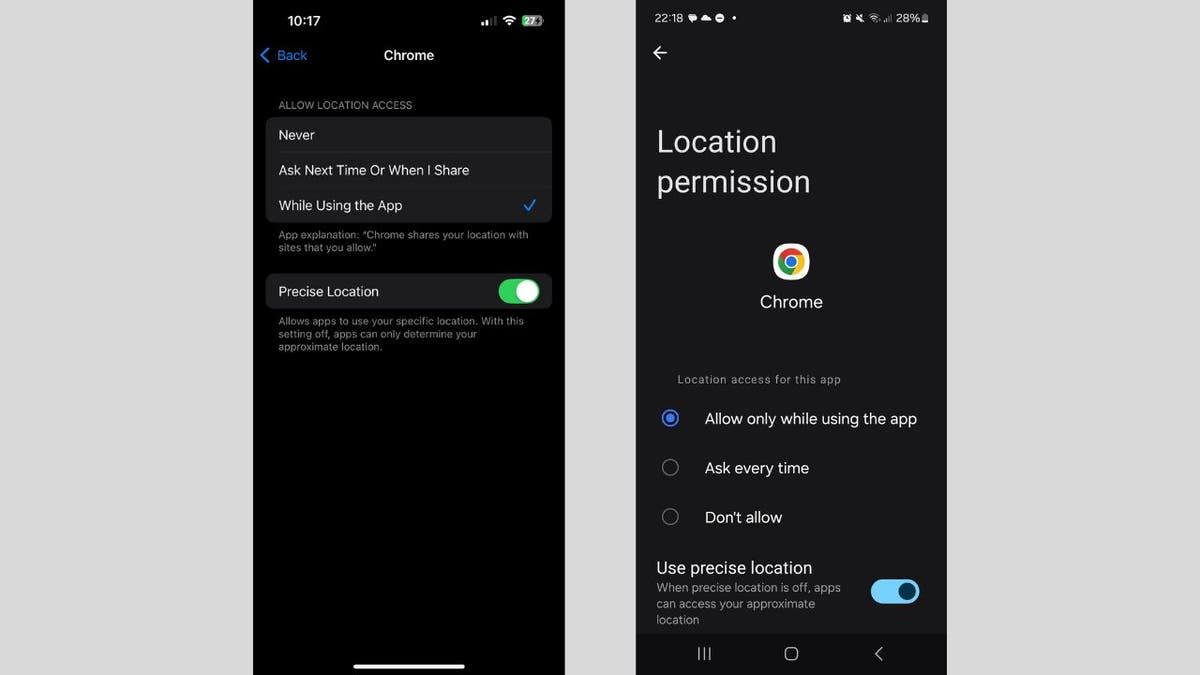
Steps to turn off the monitoring of the location on your smartphone (Kurt “Cyberguy” Knutsson)
What is artificial intelligence (AI)?
8. Change the predetermined administrator password in your router
Most routers are sent with user names and predetermined administration passwords such as “admin” or “1234”, and these are publicly available online. Computer pirates know this they often scan nets looking for unprotected rings. This is what you should do:
- Log in your Router configuration through its IP address (often 192,168.1.1 or 192.168.0.1).
- Change the Administrator user and password To something strong and unique.
- Consider using a Password administrator to generate and store complex passwords. Get more details about me The best password administrators reviewed by experts of 2025 here.
Why does it matter: Prevents intruders from kidnaping their domestic network and spying on their devices.
9. Enable WPA3 encryption in its Wi-Fi router
WPA3 is the newest wireless encryption protocol and offers much stronger protection than WPA2. If your router admits WPA3, enable it is obvious. How to verify:
- Log in your Router configuration And look below Wireless security
- If WPA3 is available, Enable it.
- If not, consider updating a newer router focused on security. Look ours Main routers for the best security 2025.
Why does it matter: Stronger encryption means that computer pirates cannot easily intercept or decipher their Wi-Fi traffic.
10. Establish a network of guests for visitors and smart devices
Their friends do not need access to their entire domestic network and neither their intelligent and timbres lights. Creating a Guest Network Add a security barrier among your personal and less reliable devices. Steps to take:
- Log in your Router configuration.
- Create a Separate guest network with his own password.
- Connect Smart devices, televisions and guests Only to this network.
- Keep your main network only for Computers and Personal Telephones.
Why does it matter: Even if an intelligent device is committed, the attacker will not have access to his main network or confidential devices.
11. Use a safe and private browser for sensitive navigation
Not all browsers treat their privacy equally. Change to a browser designed for privacy as Brave, FireNews or Duckdugo’s browser You can drastically reduce the amount of data collected on you while sailing. In addition, use Incognito/private mode For sensitive searches.
Why does it matter: It reduces digital footprints and helps prevent advertisers and data corridors from creating a profile in their navigation behavior.
Subscribe to Kurt’s YouTube channel to obtain fast video tips on how to work all its technological devices
Kurt’s Key Takeways
Staying privately online is not about being paranoid; It is about making intentional and intentional decisions. With the right tools and some small changes, you can regain control of your data in 2025. Digital privacy is always changing, so it is a good idea to verify your configuration and habits from time to time. The advantage is that for each new privacy challenge, there is generally a way to go back and maintain their safe information.
Click here to get the News application
If you want a printable verification list or want this content to become a shared infographic, let it know.
What tools and privacy methods do you use to protect your online data? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter.
Ask Kurt or tell us what stories you would like us to cover.
Follow Kurt in his social channels:
- YouTube
Answers to the most informed Cyberguys questions:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



