Payroll scam hits US universities as phishing wave deceives staff
NEWNow you can listen to News articles!
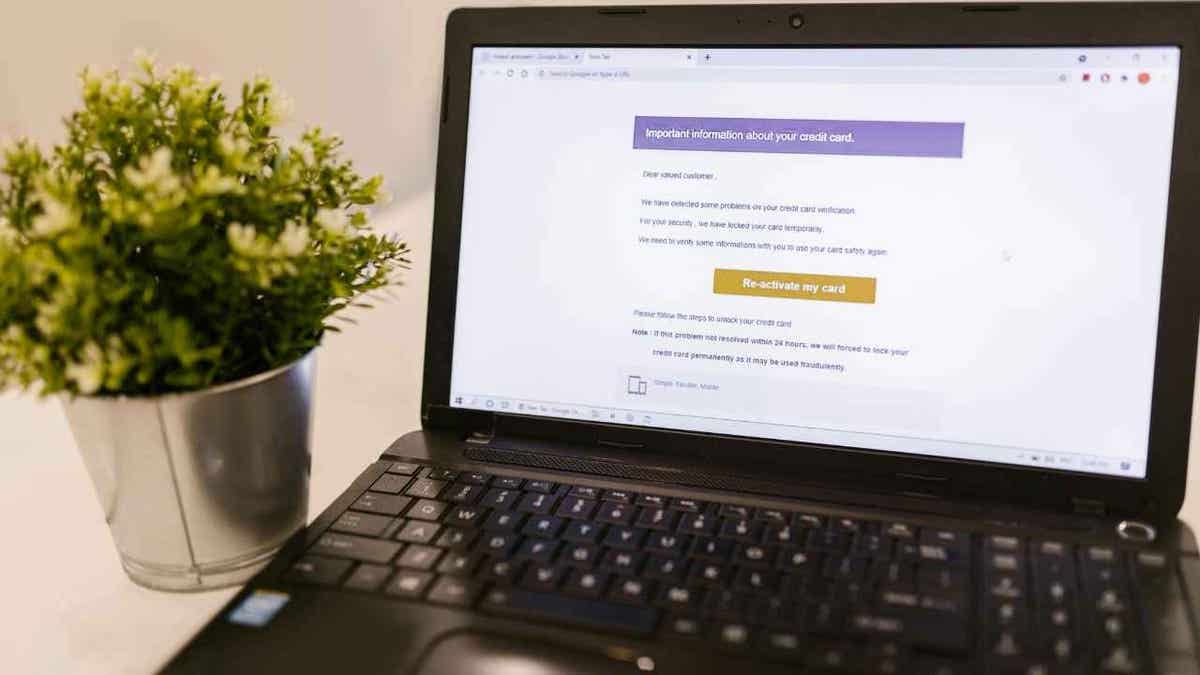
Phishing scams target all types of institutions, whether it’s a hospital, a large technology company, or even a fast food chain. Educational institutions are no exception, especially in 2025, when attackers actively direct their efforts towards them. Universities across the United States are facing a new type of cybercrime in which attackers target staff to hijack salary payments. Researchers have discovered that since March 2025, a hacking group known as Storm-2657 has been running “hack payroll” attacks, using phishing tactics to gain access to payroll accounts. Let’s talk more about this attack and how you can stay safe.
Sign up to receive my FREE CyberGuy report
Get my best tech tips, urgent security alerts, and exclusive offers delivered right to your inbox. Plus, you’ll get instant access to my Ultimate Guide to Surviving Scams, free when you join me CYBERGUY.COM. information sheet.
SCAMMERS NOW IMAGINE CO-WORKERS AND STEAL EMAIL THREADS IN CONVINCING PHISHING ATTACKS
How does the college payroll scam work?
According to Microsoft Threat Intelligence, Storm-2657 primarily targets Workday, a widely used HR platform, although other payroll and HR programs could also be at risk. Attackers start with very convincing phishing emails, carefully crafted to attract individual members of staff. Some messages warn of a sudden outbreak of illness on campus, creating a sense of urgency, while others claim that a faculty member is under investigation, prompting recipients to immediately check documents. In some cases, the emails impersonate the university president or human resources department and share “important” updates about compensation and benefits.

Phishing scams are evolving rapidly and now universities have become prime targets for payroll theft. (Kurt “CyberGuy” Knutsson)
These emails contain links designed to capture login credentials and multi-factor authentication (MFA) codes in real-time using adversary techniques in the middle. Once a staff member enters their information, attackers can access the account as if they were the legitimate user. After taking control, the hackers set inbox rules to remove Workday notifications so victims don’t see alerts about changes. This stealthy approach allows attackers to modify payroll profiles, adjust wage payment settings, and redirect funds to accounts they control, all without raising immediate suspicion.
COLUMBIA UNIVERSITY DATA BREACH AFFECTS 870,000 PEOPLE
Hackers are exploiting universities on a large scale
Hackers don’t stop at just one account. Once they control a mailbox, they use it to further spread the attack. Microsoft reports that from just 11 compromised accounts at three universities, Storm-2657 sent phishing emails to nearly 6,000 email addresses at 25 institutions. By using trusted internal accounts, your emails appear more legitimate, making recipients more likely to fall for the scam.
To maintain access over time, attackers sometimes register their own phone numbers as MFA devices, either through Workday or Duo MFA profiles. This gives them persistent access, allowing them to approve more malicious actions without needing to phishing again. Combined with inbox rules that hide notifications, this strategy allows them to operate undetected for longer periods of time.
Microsoft emphasizes that these attacks do not exploit a flaw in Workday. Instead, they rely on social engineering, the absence of robust phishing-resistant MFA, and careful manipulation of internal systems. In essence, the threat comes from human behavior and insufficient protection, not from software errors.
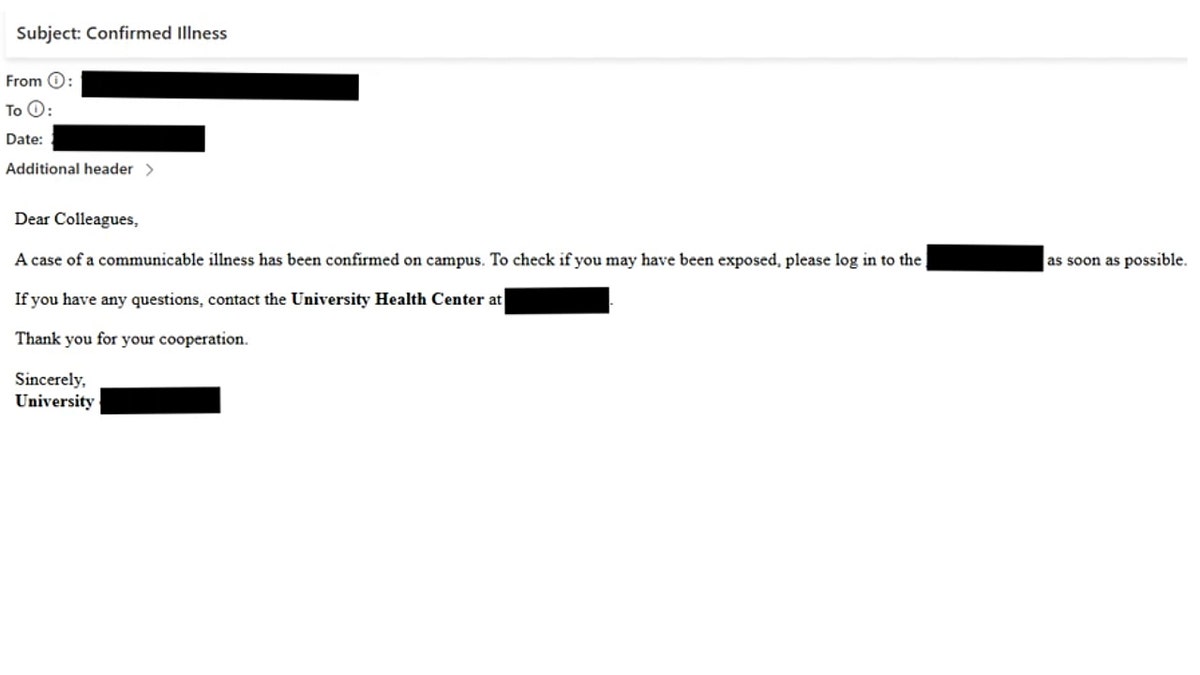
Hackers lure staff with compelling emails that mimic campus alerts or HR updates and steal login data in real time. (Microsoft)
Six Ways to Stay Safe from Payroll Scams and Phishing
Protecting yourself from payroll and phishing scams isn’t complicated. By taking some careful steps, you can make it much more difficult for attackers to gain access to your accounts or personal information.
1) Limit personal information online
The more information scammers can find out about you, the easier it will be to craft convincing phishing messages. Services that delete or monitor personal data online can reduce exposure, making it harder for attackers to trick you with targeted emails.
While no service can guarantee complete removal of your data from the Internet, a data deletion service is truly a smart choice. They are not cheap, and neither is your privacy. These services do all the work for you by actively monitoring and systematically deleting your personal information from hundreds of websites. It’s what gives me peace of mind and has proven to be the most effective way to delete your personal data from the Internet. By limiting the information available, you reduce the risk of scammers cross-referencing leak data with information they can find on the dark web, making it harder for them to target you.
Check out my top picks for data removal services and get a free scan to find out if your personal information is already available on the web by visiting Cyberguy.com.
Get a free scan to find out if your personal information is already available on the web: Cyberguy.com
2) Think before you click
Scammers often send emails that appear to come from your human resources department or university administration, warning about payroll, benefits, or urgent issues. Do not click on links or download attachments unless you are 100% sure they are legitimate. Even small mistakes can give attackers access to your accounts.
The best way to protect yourself from malicious links is to have antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe.
Get my picks for the best antivirus protection winners of 2025 for your Windows, Mac, Android, and iOS devices at Cyberguy.com.

Researchers have discovered that since March 2025, a hacking group known as Storm-2657 has been running “hack payroll” attacks, using phishing tactics to gain access to payroll accounts. (Javi Sanz/Getty Images)
3) Check directly with the source.
If an email mentions salary changes or requires action, call or email the Human Resources office or the person directly, using the contact information you already know. Phishing emails are designed to create panic and hasty decisions, so taking a moment to check can stop attackers in their tracks.
4) Use strong and unique passwords
Never reuse passwords across multiple accounts. Scammers often try to use credentials stolen from other breaches. A password manager can help you generate strong passwords and store them securely, so you don’t have to remember dozens of different combinations.
Next, check to see if your email has been exposed in previous breaches. Our #1 pick for password manager includes a built-in breach scanner that checks to see if your email address or passwords have appeared in known breaches. If you discover a match, immediately change any reused passwords and protect those accounts with new, unique credentials.
Check out the best expert-reviewed password managers of 2025 at Cyberguy.com.
5) Enable two-factor authentication (2FA)
Add an extra layer of security by enabling 2FA in all accounts that support it. This means that even if someone steals your password, you still won’t be able to log in without a second verification step, such as a code sent to your phone.
6) Periodically verify financial and payroll accounts
Even if you follow all precautions, it’s smart to monitor your accounts for any unusual activity. Quickly detecting unauthorized transactions can prevent further losses and alert you to potential scams before they escalate.
CLICK HERE TO DOWNLOAD THE News APP
Hackers will redirect payments after gaining access to users’ login information. (Kurt “CyberGuy” Knutsson)
Kurt’s Key Takeaway
Storm-2657 attacks show that cybercriminals target trust, not software. Universities are attractive because payroll systems handle money directly and staff can be manipulated through well-crafted phishing. The scale and sophistication of these attacks highlight how vulnerable even well-established institutions can be to financially motivated threat actors.
How often do you check your payroll or bank accounts for unusual activity? Let us know by writing to us at Cyberguy.com.
Sign up to receive my FREE CyberGuy report
Get my best tech tips, urgent security alerts, and exclusive offers delivered right to your inbox. Plus, you’ll get instant access to my Ultimate Guide to Surviving Scams, free when you join me CYBERGUY.COM. information sheet.
Copyright 2025 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning technology journalist with a deep love for technology, gear and gadgets that improve lives with his contributions to News and News Business since mornings on “News & Friends.” Do you have any technical questions? Get Kurt’s free CyberGuy newsletter, share your voice, a story idea or comment on CyberGuy.com.



