Chaos ransomware reaches Optima Tax relegate, 69 GB of data filtration
NEWNow you can listen to News articles!
Cyber attacks in financial services providers are no longer isolated events. In recent years, tax preparation companies, accounting software providers and data corridors have been found in the increasingly aggressive ransomware gangs. These attacks not only interrupt operations, but also expose deeply personal financial information that can feed identity theft, fraud and long -term reputation damage.
Now, Optima Tax Rave, one of the most prominent fiscal resolution in the United States, has joined that list of growing. A ransomware group called Chaos claims to have violated Optima systems, stealing 69 GB of data before encrypting internal servers.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my definitive scam survival guide, free when you join.

A woman who works on a laptop (Kurt “Cyberguy” Knutsson)
Customer case files and exposed personal information
The stolen data in the attack include what seems to be corporate documents and confidential cases of customer cases. Fiscal documents are especially valuable for cybercriminals. They often contain social security numbers, housing addresses, telephone numbers and other identifiers that can be used to commit financial fraud or impersonation.
Sources familiar with the incident said Bleeping computer This was a double extension attack. That means that chaos not only stole the data, but also encrypted optimal systems, presumably demanding a ransom in exchange for access and non -dissemination. The firm has not yet publicly commented on whether it plans to pay the rescue or notify the affected people.
Tesla Doxxing erroneously attacks non -owners throughout the United States
The attackers listed Optima in their filtration site earlier this week. Although the complete data set has not been published, the escape already raises concerns about regulatory compliance and consumer protection, especially given the sensitive nature of the company’s work.
Optima Tax Raving has not published an official statement about violation. There has been no confirmation on whether the application of the law or federal agencies are involved in the investigation. If you have ever used your services, suppose your data could be at risk.
We communicate with Fiscal Optima relegate for a comment, but we do not receive an answer before our deadline.
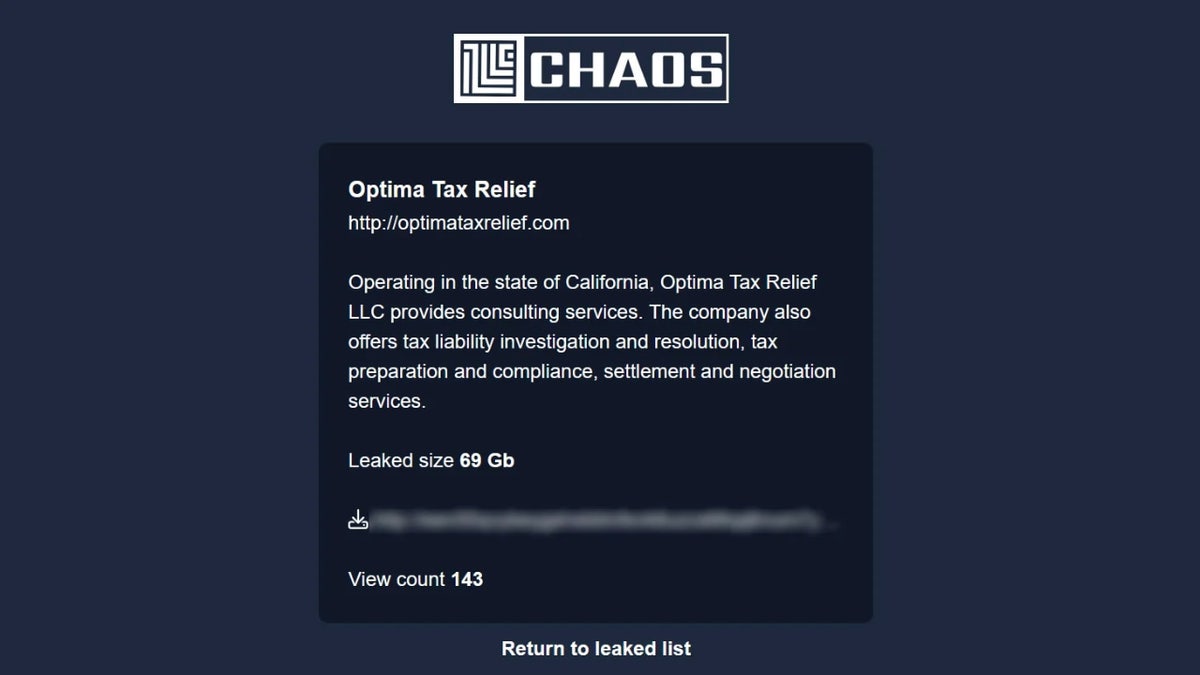
Optima’s fiscal deduction entrance at the Chaos data escape site (Bleepingcomputer)
Doublecickjacking Hack double click on account acquisitions
A new ransomware group with high -value objectives
The chaos ransomware first emerged in March 2025, when the responsibility of five separate infractions was attributed. The group is not connected to the “chaos ransomware Builder”, a DIY TOOL KIT that has been in circulation since 2021. On the other hand, it is believed that this version of Chaos is directed by a coordinated team that is strategically aimed at organizations with access to large amounts of personal identification information.
Optima is not the only high profile victim. In May, Chaos claimed to have violated the Salvation Army, although the organization has not publicly confirmed the attack or responded to media consultations.

A person moving on his smartphone (Kurt “Cyberguy” Knutsson)
Malware exposes 3.9 billion passwords in a great threat of cybersecurity
6 ways in which you can keep safe from the violation of Optima data
If your information was part of Optima’s violation or a similar one, it is worth taking some steps to protect yourself.
1. Consider identity theft protection services: Since the violation of Optima data presented personal and financial information exhibited, it is crucial to remain proactive against identity theft. Identity theft protection services offer continuous monitoring of their credit reports, the social security number and even the dark website to detect if your information is being used badly. See my advice and the best selections on how to protect yourself from identity theft.
2. Monitor your accounts and transactions: Optima’s violation could have revealed bank data to attackers, which means that they can use those details to steal their money. You must consult your accounts and transactions online regularly to obtain any suspicious or unauthorized activity. If you notice something unusual, I immediately report it to the service provider or authorities. You must also review your credit and scores reports to see if there are signs of robbery or identity fraud. To inform identity theft, visit the FTC Identitytheft.gov.
3. Contact your bank and credit card companies: Since Optima’s computer pirates could have obtained bank information and with a credit card, they could use it to make purchases or withdrawals without their consent. You must inform your bank and the credit card companies of the situation. They can help you freeze or cancel your cards, play any fraudulent position and issue new cards for you. You must also communicate with one of the three main credit reports: Equifax, Experian or Transunion, and request a fraud alert to be placed in your credit file. This will make it more difficult for identity thieves to open new accounts in your name without verification.
Get the News business on the fly by clicking here
4. Use personal data disposal services: Data violation filters a lot of information about you, and all this could end in the public domain, which essentially gives anyone the opportunity to cheat it. A proactive step is to consider personal data removal services, which specialize in monitoring and continuously eliminate their information from various databases and online websites. See my best selections to obtain data disposal services here.
Get a free scan To know if your personal information is now available on the web.
5. Have a strong antivirus software: Optima’s hackers probably have email addresses and full names of people, which makes it easier for them to send a phishing link that installs malware and steals all your data. These messages are socially designed to catch them, and catch them is almost impossible if you are not careful. However, you are not without defenses.
The best way to safeguard the malicious links is to have the antivirus software on all its devices installed. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets. Get my elections for the best antivirus protection winners 2025 for your Windows, Mac, Android and iOS devices.
6. Enable two factors: While passwords were not part of data violation, you must still enable two factors authentication (2FA). It gives you an additional security layer in all its important accounts, including email, banking and social networks. The authentication of two factors requires that you provide a second information, such as a code sent to your phone, in addition to your password when you logged in. This makes it significantly more difficult for hackers to access their accounts, even if they have their password. Enable 2FA can greatly reduce the risk of unauthorized access and protect your confidential data.
Kurt key takeway
Optima’s violation is not an isolated event, but part of a major failure to adapt to the sophistication of modern ransomware groups. When companies with access to tax and identity data are compromised, it is not just an internal problem; It becomes national. For a trust -based industry, violations such as this erode public confidence in the systems that are already tense. Attacks such as these pose new concerns about the preparation of cybersecurity of companies that handle fiscal and financial data. Unlike login credentials or email addresses, stolen fiscal information cannot be easily restored. For victims, the consequences of such rape could extend over the years.
Click here to get the News application
Do you think financial companies are investing enough in their cyber security infrastructure? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter
Ask Kurt a question or let us know what stories we would like to cover
Follow Kurt in his social channels
- YouTube
Answers to Cyberguys most facts:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



