What to do if you receive a password restoration email that you did not request
NEWNow you can listen to News articles!
You are checking your inbox or moving by your phone when something attracts your attention. It is a message about a password restoration, but never requested one.
It may have arrived by email, text message or even through an authenticator application. It seems legitimate, and could be of a service that really uses. Even so, something feels off.
Unre requested password restoration messages are often an early warning signal that someone may be trying to access their account. In some cases, the alert is real. In others, it is a false message designed to deceive it to click on a malicious link. Anyway, it means that your personal information may be at risk, and it is important to act quickly.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my definitive scam survival guide, free when you join.
10 Personal data signs are sold online
Block -speaking password (Kurt “Cyberguy” Knutsson)
Why does Electronic Password Restoration Correos receive that did not request
There are some reasons why this could happen:
- Someone is trying unauthorized access: Computer pirates often prove credentials stolen from data violations to see where they still work. If you find an account linked to your email, activating a password restoration is a way they try to obtain control.
- You are being attacked through Phishing: Scammers send emails or false password restoration text messages that seem official. These are often linked to false websites that steal their login credentials or install malware.
- You are experiencing a credential filling attack: This is when attackers use bots to flood login pages with known usernames and passwords. If something matches, they will try to restore the password and block it.
- Its authentication of two factors is blocking the login: If you receive a message from your authenticator application but did not try to log in, it means that someone has their correct password and tries to break their second protection layer.
- It may be facing a SIM exchange attempt: The two factors -based two factors’ authentication is vulnerable if someone kidnaps their phone number. If suddenly stop receiving text messages or consult password remains linked to SMS, contact your mobile supplier immediately.
What is artificial intelligence (AI)?
In some cases, the message is legitimate, as seen in email below, but the application did not come from you. That is often a sign that their login details are already in the hands of another person.
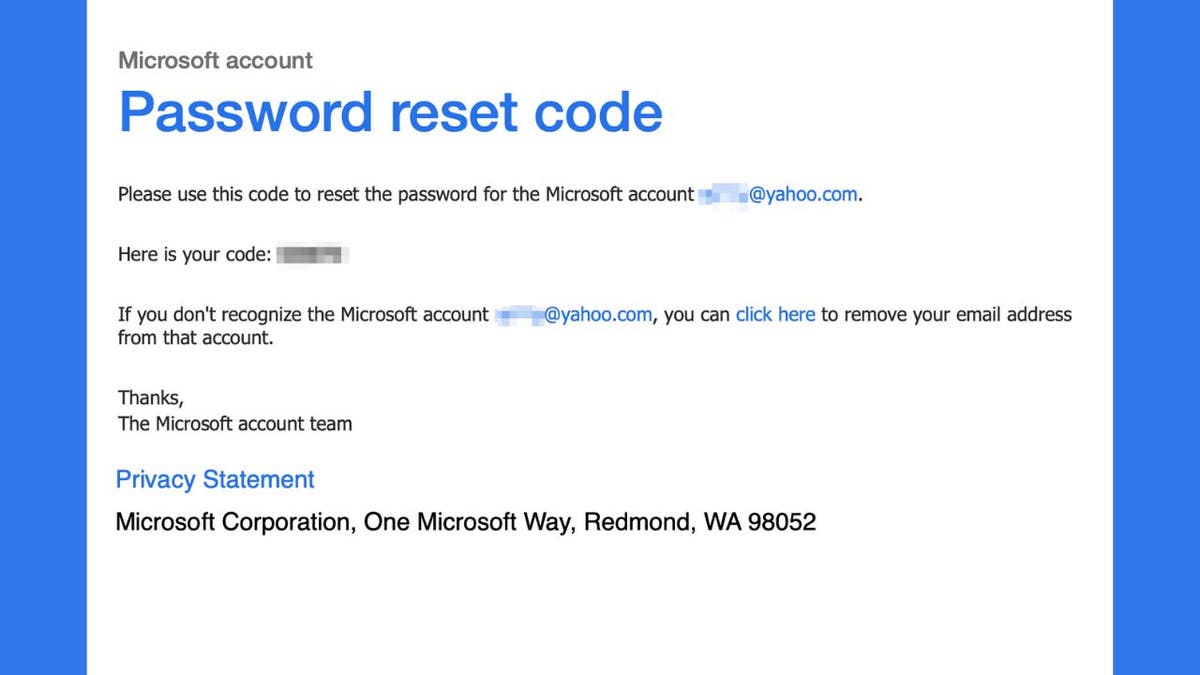
Legitimate email for Microsoft password restoration (Kurt “Cyberguy” Knutsson)
How the exchange of SIM led to a case of cyber fraud of $ 1.8 million
How to identify suspicious password restart attempts
Unre requested password restoration alerts can take several forms, each with potential fraud signs or piracy:
- Email: Most services will send a password restoration link to your inbox. If you did not request it, that is a red flag.
- Text message: You can receive a verification code or restore the link through SMS. While many companies use text -based verification, scammers also send false messages that mimic the real ones.
- Applications for authenticator applications: This is often the clearest sign that someone already has their password. If you get a 2FA message that did not activate, someone is trying to log in at this time and needs your approval to finish the process.
No matter how the alert appears, the goal is the same. Or someone is trying to deceive him to deliver his credentials, or already has his password and is trying to finish the work.

Legitimate Lye of Microsoft login (Kurt “Cyberguy” Knutsson)
1.7 billion passwords filtered on the dark website and why theirs is at risk
What to do if you receive a non -requested password restoration
If you receive a password restoration alert that you did not request, it trains it as a warning. Whether the message is legitimate or not, acting can quickly help prevent unauthorized access and stop an attack in progress. These are the steps that you must take immediately.
1. Do not click anything in the message: If the alert arrived by email or text message, avoid clicking on any link. Instead, go directly to the official site or application to verify your account. If the application was real, there will generally be a notification within your account.
2. Verify the suspicious login activity: Most accounts have a way of seeing their recent session. Look for suspicious activities such as unknown devices, strange locations or session that does not recognize. A login from a location in which you have never been could be a sign of a violation.
- Google accounts: Gonna Myacount.google.com and open the Security tab To see recent devices and activities
- Apple ID: On your iPhone, iPad or Mac, open Settings (or system configuration in Mac), touch your name At the top, move down to see your Signed devices list and touch any one unknown to select Delete.
- Microsoft accounts: Visit account.microsoft.com, loginthen go to Security > Login activity To see recent access attempts
- Banking and social networks: Look under your profile or configuration For login history or device management
3. Change your password: Even if nothing seems bad, it is a good idea to restore your password. Choose one that is long, complex and unique. Avoid reusing passwords in different accounts. Consider using a Password administrator to generate and store complex passwords. Get more details about me The best password administrators reviewed by experts from 2025 here.
4. Scan your device for threats: If someone has access to their password, there is the possibility that their device is committed. Wear Strong antivirus software To scan for Keyloggers or Spyware.
5. Report the incident: If the alert comes from a suspicious message, inform it. In Gmail, touch the three -point menu and select Reports Phishing. For other services, use the official website to mark unauthorized activity. You can also present a report in the Complaints Center for FBI Internet Crimes If you suspect a scam.

A woman who works on her laptop (Kurt “Cyberguy” Knutsson)
Steps you can take to eliminate emails from password restoration
You can take some steps to try to reduce the amount of emails you receive requesting a password restoration.
1. Check your username and password. When accessing your account, you can have a typographic error in your login information. If you try repeatedly to access your account with this error, the company that owns the account may believe that an attempt of piracy is happening, which triggers an automatic restart. If your web browser automatically fills your username and password for you, make sure this information is free of typographic errors.
2. Remove unauthorized devices. Some accounts maintain a list of authorized devices to use their account. If a hacker manages to obtain part of your personal information, you can add one of your devices to your authorized list, activating account login errors while trying to hack your password. See the list of authorized devices and delete the elements that do not recognize.
The process varies, depending on the type of account. We will cover steps for Microsoft, Gmail, Yahoo and AOL.
Microsoft
- Log in your Microsoft Actureta account.microsoft.com.
- Click your Profile icon In the upper right and select My Microsoft account.
- Move down to find the Devices Section and click See all devices.
- You will see a list of devices associated with your account. Click Show details so that everyone reviews the activity.
- If you see a device that does not recognize or no longer use, click Eliminate the device.
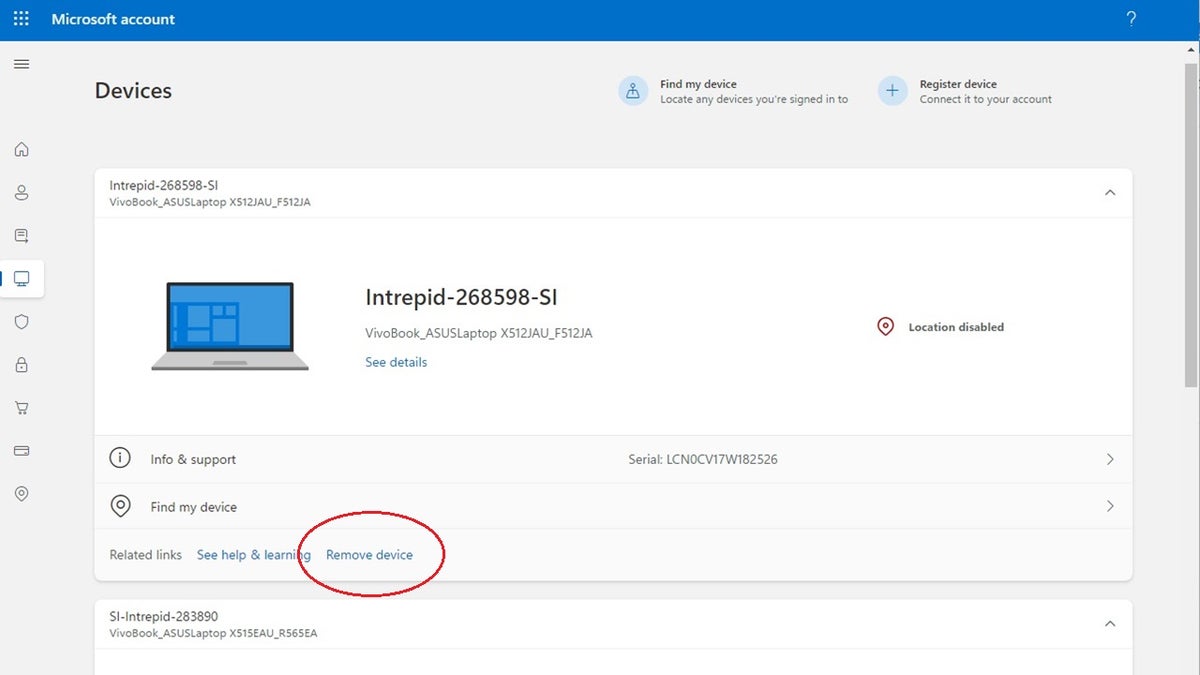
Steps to delete unauthorized devices from your Microsoft account. (Kurt “Cyberguy” Knutsson)
Gmail:
- Log in Myacount.google.com.
- Go to Security Tab in the left sidebar.
- Move down to the Your devices Section and click Administer all devices.
- Check the list of signed devices. If you see anyone you don’t recognize, click the device and select disconnect.
Yahoo:
- Go to Yahoo account security page in Help.yahoo.com/kb/account.
- Click on Recent activity.
- Check the List of devices and locations They have accessed their account.
- If you notice any unknown activity, click Eliminate either disconnect next to the suspicious device.
AOL:
- Log in your AOL ACONTETy go to Recent activity page.
- Check the sections for Recent activity, Applications connected to your account and Recent account changes.
- If you find any activity or device that does not recognize, click disconnect either Eliminate beside.
Remember to regularly verify the configuration of your account and the authorized devices to guarantee the safety of your accounts. If you suspect that any unauthorized access, it is also a good idea to change your passwords and review the recovery options of your account.
3. Order such messages for spam. If you simply prefer not to see this type of email messages, configure your email client to order messages like this in a spam folder. (Because many of them are spam, some email clients do it automatically). If you ever legitimately request a password restoration, you must remember to search the spam folder for the message.
4. Use a static IP address. Some accounts try to recognize your device through your address IP If you have a dynamic IP address, your IP address constantly changes, which means that the account may not recognize your device, activating the restart message. This often happens because it is using a VPN. See if your VPN allows you to use a static IP address.
How sure is my password? Use this test to find out
How to protect your accounts from future password attacks
Even if this was a unique scare, it is important to tighten your general safety. Here are some simple habits that contribute to a large extent:
1. Use strong and unique passwords: Use a Password administrator To create safe and unique passwords for each account. Get more details about me The best password administrators reviewed by experts from 2025 here.
2. Consider using a personal data disposal service: If you receive emails for the restoration of password of the accounts for which you do not remember subscribing, or from multiple services, there is a good possibility that your personal information is exposed in the data broker sites. These companies collect and sell their data, including their email, telephone number, housing address and even old -accounts login information. The use of a good reputation data removal service can help you identify automatically and request the elimination of your onal data from these sites. This reduces its risk of identity theft, filling of credentials, phishing and spam.
While no service can guarantee the complete elimination of your Internet data, a data removal service is really an intelligent option. They are not cheap, and it is not your privacy either. These services do all the work by you by actively monitoring and systematically erasing your personal information from hundreds of websites. It is what gives me peace of mind and has proven to be the most effective way to erase your personal internet data. By limiting the available information, it reduces the risk of cross -references data of infractions with information they can find in the dark network, which makes it difficult to be pointed out. See my best selections to obtain data disposal services here.
Get a free scan To find out if your personal information is now available on the web
3. Turn on the authentication of two factors (2FA): Enabling 2fa It is one of the most effective ways to stop unauthorized access, even if someone has their password. When 2FA is active, anyone who tries to log in must also complete a second check step, usually through an application on your phone. If an attacker triggers a login attempt, he will receive a message to approve or deny it. This gives you the power to block the attempt in real time and confirms that 2FA is working as planned.
4. Install strong antivirus software: Install strong antivirus software to catch malware before causing damage. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets. Get my elections for the best antivirus protection winners 2025 for your Windows, Mac, Android and iOS devices.
5. Check your account configuration: Make sure your recovery phone number and email are current. Eliminate obsolete or unused backup methods.
6. Keep your updated software: Keep your software and applications of your device up to date to patch security vulnerabilities that attackers often explode.
7. Use a VPN to protect your activity online: Avoid public Wi-Fi or use a VPN to protect your information by navigating non-safe networks. Consider using a VPN to protect against computer pirates that also sink on your device. The VPNs will protect it from those who wish to track and identify their potential location and the websites that visit. To obtain the best VPN software, see my expert review of the best VPN to navigate on the private web in your Windows, Mac, Android and iOS devices
Kurt’s Key Takeways
It is easy to brush an unexpected message of password restoration, especially if nothing else seems to be out of place. But these alerts are often the digital equivalent of a blow to the door when you did not wait for anyone. Whether it is a hacker that investigates a shape or a scammer that tries to prime it, the smartest movement is to treat each unexpected security message as a call for attention. Taking only a few minutes to verify your login history, secure your accounts and update your passwords can make a difference. Cybersecurity is no longer just for experts. It is an integral part of everyday life. And the more proactive you are now, the less likely it is that I deal with damage control later.
Click here to get the News application
Are technology companies doing enough to protect users from password threats, or are they putting too much responsibility for people? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter
Ask Kurt a question or let us know what stories we would like to cover
Follow Kurt in his social channels
- YouTube
Answers to Cyberguys most facts:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



