Application of pirated tea as photos of women, IDS and even dms filtered online
NEWNow you can listen to News articles!
The dating sites that are billed as discreet and private have often not fulfilled that promise. Let’s take Ashley Madison, for example, a dating website specifically for people looking for extramarital issues, who suffered a massive data violation in 2015. The computer pirates leaked the data of 32 million users, including personal information, emails and financial details, which caused public indignation, demands and suicides.
Now, an appointment safety application called TEA has suffered its own violation, compromising selfies, identification of photos and images of publications, comments and direct messages within the application.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my definitive scam survival guide, free when it joins me Cyberguy.com/newsletter.
Dior data violation exposes the personal information of US clients

What you need to know about the violation of tea data
TEA was launched in 2023 as an “appointment security” application based in the USA. UU. For women, which requires verification through selfies and identification issued by the Government. The identification requirement was gradually eliminated that year. The application won viral impulse in July 2025, reaching the upper part of the US Application Store and accumulating millions of users
On July 25, users in 4Chan discovered a public access firm storage cube containing tea users data (through 404Media). According to the reports, a publication exclaimed: “Driving licenses and face photos!
Later, TEA confirmed that the violation involved unauthorized access to an inherited database containing approximately 72,000 images, including 13,000 selfies and identification photos, and 59,000 images of publications, comments and messages. These belonged to users who registered before February 2024.
The leadership of TEA issued public statements that confirmed the violation of the image and said that the data came from older systems that did not migrate to the current safe infrastructure. TEA also declared that email addresses or telephone numbers were not exposed and that only inherited users were affected.
The new revelations of the independent researcher Kasra Rahjardi and the reports of 404 Media showed that the violation extended far beyond the images since approximately 1.1 million direct messages (DMS) ranging from early 2023 to July 2025 were also exposed. These included highly confidential conversations about abortions, traps, telephone numbers, meetings information and more.
What is artificial intelligence (AI)?
In response, TEA disabled its DM system and felt outside the affected messaging system. The company announced that it found no intrusion evidence in other parts of its infrastructure.
Cyberguy contacted tea to comment, but had not received an answer at the time of publication.
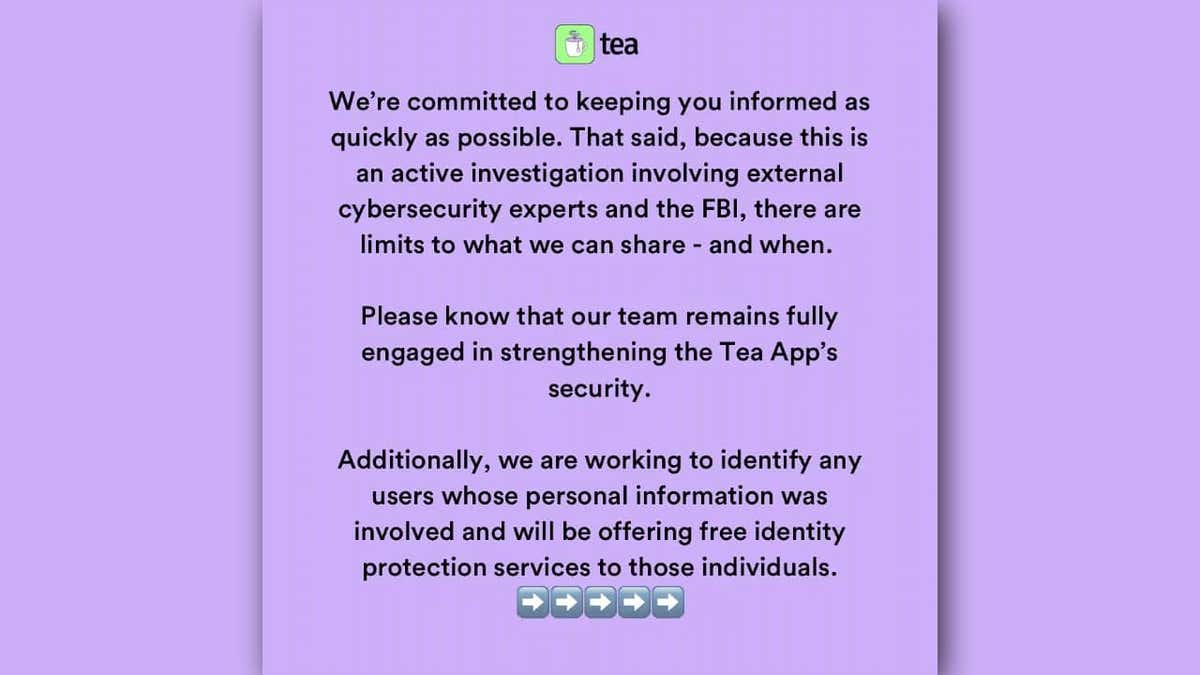
Tea application customer notice. (Tea)
Why the violation of tea application is devastating for users
The violation of tea data is a nightmare for all its users, and only shows how irresponsible are companies by promoting privacy.
Tea positioned itself as a safe space for women to share intimate experiences and then failed in the most important promise it did, which is protecting that intimacy.
This was not just user names or email addresses. We are talking about government identifications, selfies and 1.1 million private DMs containing confessions, details of the relationship and deeply personal issues such as assault and abortions. That is the type of rape that you cannot walk back. Once those images and conversations are in nature, they are effectively permanent.
Tea was not a generic social application. It was marketed as a “dating” platform for women, which means that users had a reasonable expectation of privacy protections higher than the standard.
These leaks came first to a misogynist forum. The victims were not only exposed, they were immediately subjected to harassment campaigns, Doxxy attempts and their faces and stories circulating without consent.

A woman who uses an application on her smartphone. (Kurt “Cyberguy” Knutsson)
6 ways in which tea data violation can be protected
If you have ever used tea or even registered, it is important to take action now. There are six steps here to help protect your privacy and limit the consequences.
1) Register for identity theft protection
If your identification was part of the escape, you are at risk of impersonation, and a service protection service can help you stay safe. These services alert him about suspicious activities such as new credit consultations, account openings or changes in his financial records, helping him act before the damage extends.
See my advice and the best selections on how to protect yourself from identity theft in Cyberguy.com/ididentitytheft.
2) Use a personal data elimination service
Selfies or filtered names can end in sites for searching people or shaded databases. A personal data removal service can help you eliminate all this personal internet information. While no service promises to eliminate all its Internet data, having an elimination service is excellent if you want to constantly monitor and automate the process of eliminating your information from hundreds of sites continuously for a longer period of time.
See my best selections to obtain data removal services and get a free scan to find out if your personal information is now available on the web visiting Cyberguy.com/delete.
Get a free scan to find out if your personal information is already on the web: Cyberguy.com/freescan.
Get the News business on the fly by clicking here
3) Change your passwords and use two factors authentication (2FA)
The attackers often reference the user names and the reused passwords on the Internet, even if their login was not part of the filtration. Update of your passwords and enabling two factors authentication In all accounts there is a basic but crucial defense. Consider using a password administrator, which stores and generates complex passwords, reducing the risk of password reuse.
See the best password administrators reviewed by 2025 experts in Cyberguy.com/Passwords.
4) Be alert to phishing and blackmail attempts and use strong antivirus software
After high profile, it is common for victims to receive threatening messages. Do not respond. Do not click links. Report the message and block the sender. If you feel insecure, communicate with local authorities of cyber crimes or a digital rights organization.
The best way to safeguard the malicious links is to have a strong antivirus software installed on all its devices. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets.
Get my elections for the best 2025 antivirus protection winners for their Windows, Mac, Android and iOS devices in Cyberguy.com/Lockupyoutech.
5) Verify where your images are shared
Use inverse image search tools such as Google Images or Pimeyes to see if your face has been published elsewhere. If you find something, documently. Inform it on the platform and avoid committing directly to who shared it.
6) Present a complaint to regulators
If you think your data were badly managed, you can file a complaint to:
- The Federal Trade Commission (FTC) in Reportfraud.ftc.gov
- His State Attorney General either Data Protection Authority
This adds pressure on the company to assume responsibility and can help prevent the improper use of your data.
Click here to get the News application
Kurt key takeway
It is a pity that a platform promised privacy and to provide women with a space to open did not strive to protect the data it had. If it were any other type of application, this could still be contained. But one in which people share confidential information put users in real danger. We are already seeing people harass those whose data leaked, and will probably worsen from here.
Do you think that applications that handle confidential data should be maintained with stricter safety standards? Get us knowing in Cyberguy.com/contact.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my definitive scam survival guide, free when it joins me Cyberguy.com/newsletter.
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



