Elmo Hack exposes serious cybersecurity threats on social networks
NEWNow you can listen to News articles!
While traveling with X (previously Twitter), it is possible that he meets Elmo, the adorable red monster appreciated by children and parents, sharing cheerful and friendly content for the family. However, recently, Elmo’s official account had suddenly published hate speech, racist insults and political attacks. This shocking violation transformed a beloved food into a source of confusion and pain.
Sesame Workshop, the team behind Elmo, quickly acted to eliminate offensive publications, but for millions of fans, the damage had already been done. This was much more than a typical trick. It represented the digital disfiguration of one of the most reliable children’s icons. This incident emphasizes that in the current cyber landscape, it does not take into account, not even the safest, it is immune to the attackers.
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my final scam survival guide, free when I join me Cyberguy.com/newsletter
Elmo X Pirateada account shocks users with ‘Kill All Jews’ and ‘Publish the files’ publications

Elmo’s official X verified account (@Elmo in x)
Cybersecurity risks in social networks for trusted brands
Computer pirates yearn for scope and attention, and few objectives offer more than a beloved global brand. When the attackers take over the control of an account with hundreds of thousands of followers, they get immediate access to amplify their message, whether misinformation, hate speech or target harassment. Elmo’s incident was not about stealing resonance data or accounts; It was about causing chaos, planting division and the rupture of trust.
For years, Elmo’s online voice was synonymous with joy and support. With a single violation, that reputation was mistreated, since the followers questioned how such ugliness could appear of such a reliable character. The reputation of the brand, built for decades, was compromised in minutes.
As a Sesame workshop declared in response, “Elmo’s X account was briefly pirate on an external part despite the established security measures. We firmly condemn the anti -Semitic and racious content, and the account has since been insured since then. These publications in any way reflect the values of the Sesame or Sesame Street workshop, and no one in the organization was involved.”
This incident underlines the importance of solid cyber security measures, especially when trust brands serve as platforms for millions worldwide.
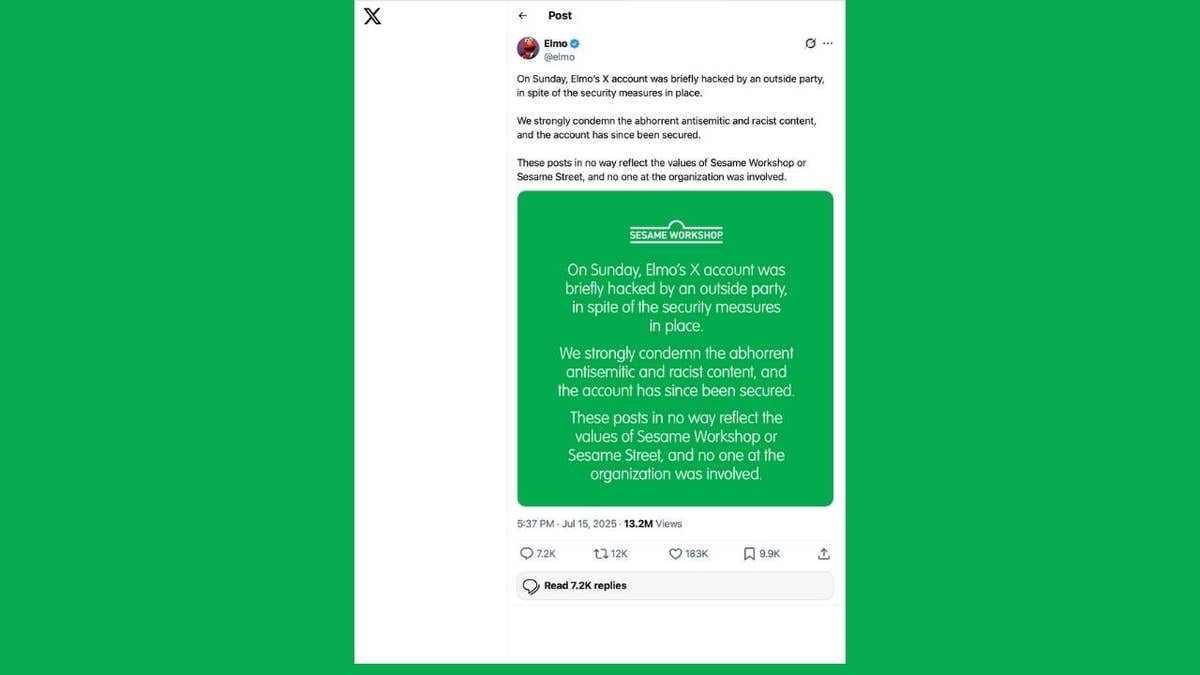
Sesame workshop statement after Elmo X Hack (ELMO X Account)
Why social media accounts are pirate (even “strong”) security
To better understand what happened, we resorted to Daniel Tobok, CEO of Cypfer, a world leader of cybersecurity and response to incidents. Daniel has spent more than 30 years guiding organizations through the main cyber events.
“Unfortunately, many credentials are harvested and sold on the dark website between the groups of actors of different threats despite the safe passwords or the barriers of MFA. Maybe someone lost their password or an administrator was kept in a laptop that was part of another violation. Once those passwords are collected, they are exchanged or sold,” Daniel explained.
While brute force attacks still occur, most criminals do not waste time hitting complex passwords. On the other hand, simpler routes exploit: snatching passwords from old violations, directly go to users or kidnap the password vaults, especially those administered by social media administrators.
“Brute force attacks make a lot of noise and can activate alerts. It is no longer the most popular strategy because it is very noisy,” adds Tobok.
Warning signals that your social media account can be pirate
Unfortunately, you may not get a warning that your account is being attacked.
Tobok points out: “There really is no software that notifies you. That usually comes through the MFA channels.
Computer pirates can even configure rules that write safety notifications away from their entrance tray, leaving you completely unconscious that anything is wrong, until it is too late.

A woman moving on social networks on her smartphone (Kurt “Cyberguy” Knutsson)
Safety errors of common social networks to avoid
Computer pirates tell you to be complacent. Daniel calls the traps to avoid:
- Do not verify your account
- Reuse or not rotate passwords
- Omit MFA (multifactor authentication)
- Assuming “it will not happen to us”
More alarmingly, Daniel added: “The information of most people has already committed at some point. There are more than 4.8 billion passwords that circulate on the dark website at this time. And, finally, never reuse the same password on multiple platforms. I know it is tedious, but this is how adequate hygiene is seen.”
What is artificial intelligence (AI)?

A man by moving on social networks on his phone (Kurt “Cyberguy” Knutsson)
What to do if their social networks are compromised
Act quickly. Here is Daniel’s step by step:
“If you still have access, change your password immediately. Most threat actors, once they are inside, will immediately change the password and email linked to the account so that you can take total control. If you are blocked, you must communicate with the platform and provide proof that it is your account. Request that you close or help you recover the good news, most of the platforms will act quickly, especially if you will inform you. Your account of your account.
Key steps to protect your social media accounts
Protecting your social media accounts is more important than ever. Follow these steps to strengthen your cybersecurity and keep the computer pirates out:
1. Use strong and unique passwords
Create passwords with at least nine characters, mixing uppercase, lowercase, numbers and symbols. Never reuse passwords on the platforms and update regularly to obtain maximum protection. Consider using a password administrator, which stores and generates complex passwords, reducing the risk of password reuse. In addition, use a password administrator instead of sending passwords through unbiling messages. Password administrators allow you to share credentials when absolutely necessary and help prevent leaks safely.
See the best password administrators reviewed by 2025 experts in Cyberguy.com/Passwords
2. Enable multifactor authentication (MFA)
Always activate MFA to add an additional login protection layer. This makes it much more difficult for unauthorized users to get access, even if your password is compromised.
3. Configure suspicious login activity alerts
Take advantage of account alerts and limit the failed login attempts to quickly detect intruders. Regularly check these alerts so that I can respond immediately if something looks at.
4. Verify your accounts with the platform
Request the official verification of the account when possible to add additional protection and facilitate recovery. Verification can also dissuade impersonation and generate trust with your audience.
5. Update account recovery information
Check and keep the recovery email and the updated telephone number to recover access if necessary. Unced information could block it just when you need to recover your account more.
Get the News business on the fly by clicking here
6. Check access to third -party application
Eliminate applications or services that you no longer use; These can become weak points if they are compromised. Regularly audit the connected applications to ensure that your data is not exposed through unused integrations.
7. support its content and followers
Use characteristics of the platform or trusted tools to make an important data backup in case of account or block loss. This simple step can be a lifeguard if you ever lose access or your data are accidentally eliminated.
8. Use strong antivirus software
Install strong antivirus software on all devices used to access social networks. Regular updates and real -time scan protect it from malware and phishing that could compromise their accounts. The best way to safeguard the malicious links that install malware, which potentially access their private information, is to have an antivirus software installed on all its devices. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets.
Get my choices for the best 2025 antivirus protection devices for your Windows, Mac, Android and iOS devices in Cyberguy.com/Lockupyoutech
9. Consider a data removal service
Reduce your fingerprint and minimize risk through the use of services that eliminate your personal information information and people search sites, especially after rape. These services make it difficult for criminals to collect confidential data used in social engineering attacks. While no service can guarantee the complete elimination of your Internet data, a data removal service is really an intelligent option. They are not cheap, and it is not your privacy either. These services do all the work by you by actively monitoring and systematically erasing your personal information from hundreds of websites. It is what gives me peace of mind and has proven to be the most effective way to erase your personal internet data. By limiting the available information, it reduces the risk of cross -references data of infractions with information they can find in the dark network, which makes it difficult to be pointed out.
See my best selections to obtain data removal services and get a free scan to find out if your personal information is now available on the web visiting Cyberguy.com/delete
Get a free scan to find out if your personal information is already on the web: Cyberguy.com/freescan
10. Perform regular safety configuration audits
Periodically review your privacy and security configuration of your social networks to ensure that they coincide with your current needs. Platforms often add new configurations and features, and stay updated gives you the best protection.
11. Be careful using public wi-fi
Avoid logging into accounts in Public wi-fi or always use a VPN. Public networks facilitate computer pirates to intercept their information.
To get the best VPN software, see my rev Expert from the best VPN to navigate the web in private on its Windows, Mac, Android and iOS devices Cyberguy.com/vpn
12. Remove former employees or administrators
Regularly audit access to the account and revoke permits for anyone who no longer needs it. This ensures that only trusted people can publish or make changes in their name.
Click here to get the News application
Kurt’s Key Takeways
Elmo’s trick shattered more than a simple cheerful digital person. He reminded us that no brand, regardless of how reliable, is immune to today’s cyber threats. In an environment where trust is built on Tweet and lost in a few moments, protecting our digital presence has never been more urgent. The safety of social networks is everyone’s responsibility. Take measures before becoming the next viral lesson on what you should not do.
Do you think social media companies are doing enough to protect users and brands from evolved cyber security threats? Get us knowing in Cyberguy.com/contact
Register for my free Cyberguy report
Get my best technological tips, urgent security alerts and exclusive offers delivered directly to your inbox. In addition, you will get instant access to my definitive scam survival guide -… free when you join me Cyberguy.com/newsletter
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is an award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Morning in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



