How hackers are entering Apple devices through AirPlay
Unique News to access this content
You have reached its maximum number of articles. Log in or create an account for free to continue reading.
When you enter your email and press continue, you accept the terms of use and the privacy policy of News, which includes our financial incentive notice.
Please enter a valid email address.
Apple’s AirPlay was designed to facilitate life, allowing users to transmit music, photos and videos from iPhones and macbooks to televisions, speakers and other compatible devices with only one touch. But now, cybersecurity researchers have revealed that this same convenience may be opening the door to computer pirates. A new set of vulnerabilities, collectively called Airborne, could convert the devices enabled for the plane into stealthy entry points for malware and network infiltration.
Usa to the “Cyberguy Free Report: Obtain my expert technical advice, critical security alerts and exclusive offers, in addition to instant access to my free “Survival guide for definitive scam “ When you register.

A person holding an iPhone (Kurt “Cyberguy” Knutsson)
What you need to know
Researchers of the cybersecurity firm with headquarters in Tel Aviv Oligo recently revealed Airborne, a group of safety failures in the Apple AirPlay patented protocol. These errors exist mainly in the AirPlay Software Development Kit (SDK) used by third -party manufacturers to carry airplay support to smart televisions, speakers and other media devices. Security failures mean that if a hacker is on the same Wi-Fi network as a vulnerable device, they can kidnap it without touching the device.
From there, the attackers could move laterally inside a home or corporate network, silently jumping from one device to another. They can install malware or ransomware, interrupt operations or even block users of their own systems. In some cases, committed devices could be added to a botnet, a network of kidnapped machines working in unison for larger attacks. And because many intelligent devices are equipped with microphones, computer pirates could even turn them into tools to listen to hiding and surveillance.

A woman moving on her smartphone (Kurt “Cyberguy” Knutsson)
200 million social media records filtered in data violation x Major X
What is Apple doing with errors in the air?
Apple has already paveled airborne errors on its own devices and has issued updates to external suppliers. However, researchers warn that many third -party products enabled by plane, possibly tens of millions, can never receive a solution, either because they do not automatically update or because suppliers are slow or are not willing to release security patches.
A remarkable demonstration of Oligo showed how easily he took care of a Bose speaker to show the company logo, demonstrating how simple it could be for a hacker to obtain control in silence. Although Bose was not specifically directed, the example highlights the broadest risk. Any non -flicked device that uses Airplay SDK could be a gateway for malicious actors.
The researchers also discovered that Apple Carplay is affected. While exploiting it would be more difficult and would require a Bluetooth or USB match, more than 800 car and truck models are potentially vulnerable.
HERTZ data violation exposes customer information
How to update your iPhone software
- Gonna Settings
- Tap General
- Click Software update
- Download and install The last update.
- Your iPhone will do it restart once the update is completed.
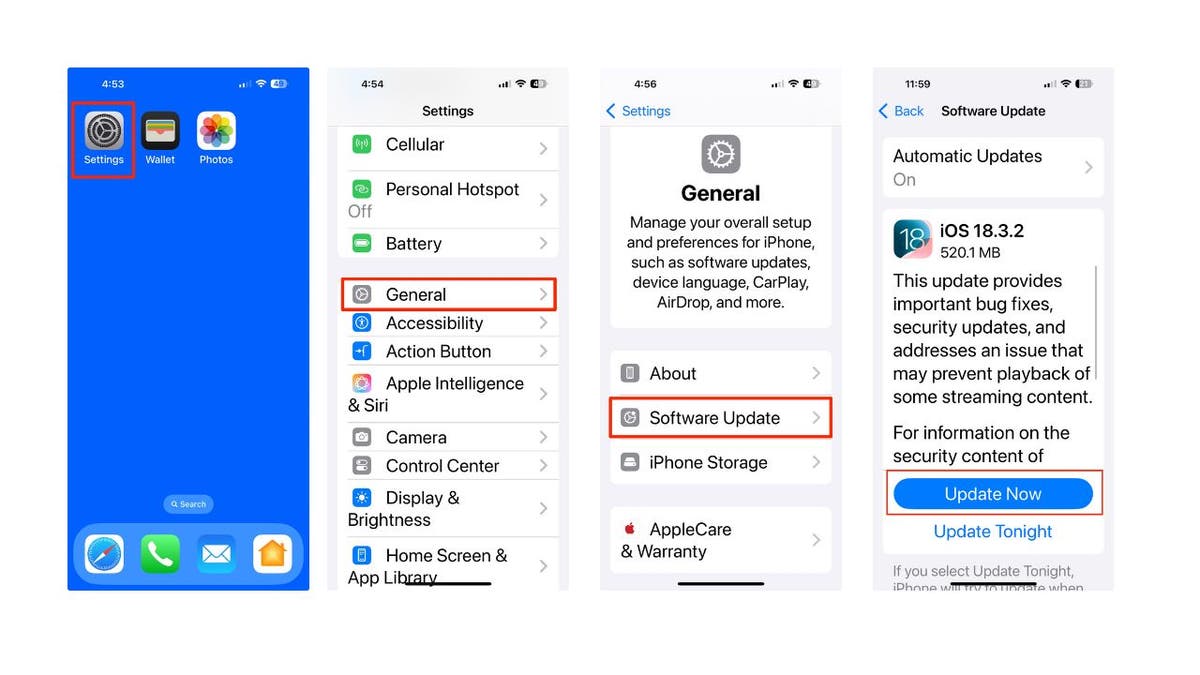
Steps to update your iPhone software (Kurt “Cyberguy” Knutsson)
How to update all your devices and keep them safe
5 ways to protect themselves from computer pirates
1) Configure a separate Wi-Fi network for smart devices: Most modern routers allow you to create multiple networks. Use this function to maintain its intelligent domestic devices, such as speakers, televisions or receptors enabled for AirPlay in a “IoT” network (Internet of Things). Keep this separated from your main devices, such as phones, laptops and work computers. This segmentation ensures that even if a hacker gets access to a vulnerable intelligent device, it cannot easily reach more critical or sensitive devices on the primary network.
2) Disable AirPlay when I don’t actively use it: AirPlay is designed to always be on and discovered, which makes it convenient, but also leaves it exposed. If you rarely use AirPlay or only use it occasionally, enter your device configuration and add it completely. On Apple devices, AirPlay settings can be found in “General” or “AirPlay & Homing”. For third -party devices, see your complementary applications or manuals. Turning Airplay eliminates it as an open door for attackers.
3) Avoid using AirPlay in public Wi-Fi or unknown and use a VPN: One of the key conditions to exploit vulnerabilities in the air is that the attacker must be in the same Wi-Fi network as the destination device. This makes public Wi-Fi networks in places such as coffees, airports, hotels or shared work spaces. If you need to use your device in such environments, avoid the foundry, transmission or pairing with smart devices.
Consider using a VPN to protect against computer pirates that also sink on your device. The VPNs will protect it from those who wish to track and identify their potential location and the websites that visit. A reliable VPN is essential to protect your online privacy and guarantee a safe high -speed connection. For the best VPN Software, see my expert review of the best VPN to navigate on the web in private on its Windows, Mac, Android and iOS devices.
4) Strengthen and ensure your home’s Wi-Fi network: Make it more difficult for attackers to access their domestic network. Use a solid and unique password for your Wi-Fi that is different from your other account credentials. Make sure the firmware of your router is updated and that the encryption is configured on WPA2 or WPA3. Avoid older and less safe options such as WEP or open networks. Disable functions as WPS, which are designed for easy settings, but can also make your network more vulnerable. If possible, disable Universal Plug and Play (UPNP) and similar characteristics that make all devices on your network easy to discover. In addition, consider using a password administrator to generate and store complex passwords. Get more details about me The best password administrators reviewed by experts of 2025 here.
5) Limit the permits and exposure of the device: Intelligent devices with airplay support often include characteristics such as microphones, automatic matching and remote access. Check the configuration of each device and disable the characteristics that you do not actively use. For example, if your smart speaker has a microphone, but never uses voice commands, turn off the microphone or cover. The fewer functions have exposed a device, the less opportunities a hacker has to exploit it. If your router admits it, use Firewall rules at the device level to limit what services or Internet connections can access your smart devices.
Kurt key takeway
Apple likes to market itself as the option for privacy and safety, but vulnerabilities in the air show that the company’s devices are far from bulletproof. While they repaired their own products, millions of third -party airplay devices are still open to the attack. It is clear that Apple’s control over its ecosystem is not as tight as you would like you to believe. If they really want to be privacy leaders, they must intensify and solve these problems in all areas, not only when it suits them.
Do you trust Apple’s claims about privacy and security after reading this article? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter.
Ask Kurt a question or let us know what stories we would like to cover.
Follow Kurt in his social channels:
- YouTube
Answers to the most informed Cyberguys questions:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
- The best gifts for mom 2025
Copyright 2025 Cyberguy.com. All rights reserved.



