More than 2,800 websites used to spread the AMOS malware
Ransomware gangs once prospered in infected email attachments and false invoices, but safety expert users and hardened mail link doors have weakened those tactics. The attackers are now focusing on a more subtle trick that goes to the small verification box labeled “I am not a robot” that most people click without thinking.
A generalized campaign known as Macreaper has committed more than 2,800 legitimate websites and redirect visitors to an infection process specifically designed for Apple computers. The operation is based on visual confidence signs, including a convincing falsification of Google’s recaptcha, along with the hidden standard code that ends with the installation of atomic malware macos Stealer, an infosteter of data collection distributed through Telegram.
Usa to the “Cyberguy Free Report: Obtain my expert technology advice, critical security alerts and exclusive offers, in addition to instant access to my Survival guide for the free final scam “ When you register!

A woman who works on her laptop (Kurt “Cyberguy” Knutsson)
How does the attack develop?
When a Mac user visits one of the compromised websites, he does not see the page they expected. Instead, the site shows a full screen imitation of the Google family recaptcha box.
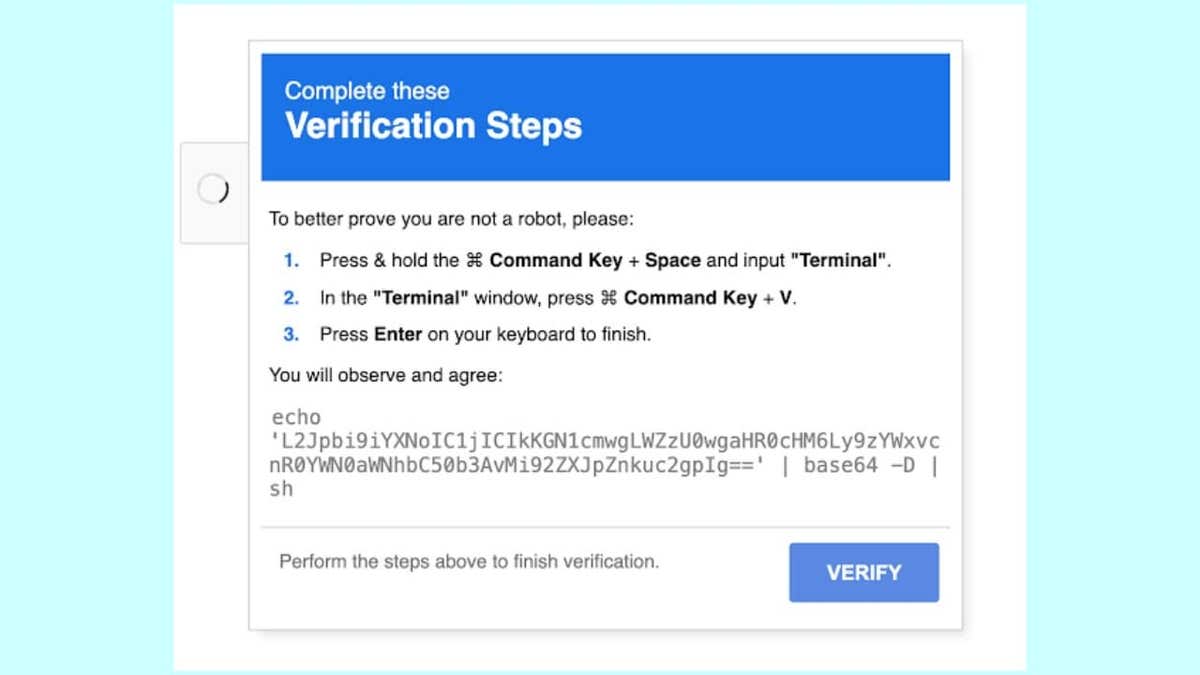
This false recaptcha seems harmless, simply asking the user to click “I’m not a robot.” However, when the user clicks on the box, a command hidden to their clipboard is silent. Immediately afterwards, the page shows a friendly, complete message with visuals of family macOS keyboard shortcuts, explicitly instructing the user to open terminal and paste what just copied. If the user follows these instructions, the download and executes the malicious file known as Atomic Macos Stealer (AMOS).
This trick is specifically aimed at Mac users. The website verifies the visitor operating system and only activates the attack if it detects macOS. For Windows or Linux users, the site behaves normally. Researchers have called this “clickfix” infection method, referring to the only click that starts the attack chain.
In the center of this campaign is Amos, a sophisticated piece of malware that has become noticeable in cyber crimes circles. Amos is available to rent on Telegram, with some versions that cost the attackers up to $ 3,000 per month. Once installed, masters can steal a wide range of confidential data: you can extract Wi-Fi passwords and applications stored in the keychain, collect browser cookies and automatic approach data, list system information and scan through personal folders such as desktop and documents. It is also able to identify and go to more than 50 types of cryptocurrency wallets.
False recaptcha (cyber security news) (Kurt “Cyberguy” Knutsson)
The hidden costs of free applications: your personal information
Mac are not as safe as Apple wants you to create
Macreaper challenges two widely sustained beliefs. The first is that Captcha’s daily controls are only harmless speed potholes. The second is that Macos provides a built -in level of security that keeps most of the attackers at bay. Actually, a single click can expose keychain credentials, active browser sessions and cryptocurrency wallets.
These are exactly the types of objectives that attract groups of credentials and cybercriminals based on profits. Because the user triggers the attack, many network monitoring tools treat traffic in a normal way, leaving safety equipment with little to investigate. In environments where Mac and Windows machines share identity systems, a compromised MAC can open access to single login portals, cloud storage and even production code bases.

A woman who works on her laptop (Kurt “Cyberguy” Knutsson)
Spotify reproduction lists are being kidnapped to promote pirate software and scams
6 ways in which it can be kept safe from Macreaper Attack
To protect themselves from the evolutionary threat of the Macreaper attack, which continues to address users through sophisticated social engineering tactics, consider implementing these six essential security measures.
1) Be skeptical of the captcha indications: Captcha’s legitimate evidence never requires copying commands or sticking anything to the terminal. If a website tells you to do this, it is likely to be a scam. Close the page immediately and avoid interacting with it.
2) Do not click links from emails not verified and use strong antivirus software: Many Macreaper attacks begin with phishing emails that are passed through reliable services. Always check the sender before clicking on the links. If an email seems urgent or unexpected, go directly to the company’s official website instead of clicking any link inside the email.
The best way to safeguard the malicious links that install malware, which potentially access their private information, is to have strong antivirus software installed on all its devices. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets. Get my elections for the best antivirus protection winners 2025 for your Windows, Mac, Android and iOS devices.
3) enable two factors authentication: Allow two factors authentication whenever possible. This adds an additional security layer when requiring a second form of verification, such as a code sent to your phone, in addition to your password.
4) Keep updated devices: Regularly Update of your operating system, browser and safety software He assures that he has the last patches against known vulnerabilities. Cybercounts exploit obsolete systems, so allowing automatic updates is a simple but effective way to stay protected.
5) Monitor your accounts for suspicious activity and change your passwords: If you have interacted with a suspicious website, a Phishing email or a false login page, see your online accounts to obtain any unusual activity. Look for unexpected login attempts, unauthorized password remains or financial transactions that you do not recognize. If something seems off, change your passwords immediately and report the activity to the relevant service provider. In addition, consider using a password administrator to generate and store complex passwords. Get more details about me The best password administrators reviewed by experts of 2025 here.
6) Invest in a personal data elimination service: Consider using a service that monitors your personal information and alerts it to possible infractions or the unauthorized use of your data. These services can provide early warning signals of identity theft or other malicious activities resulting from macreaper or similar attacks. While no service promises to eliminate all its Internet data, having an elimination service is excellent if you want to constantly monitor and automate the process of eliminating your information from hundreds of sites continuously for a longer period of time. See my best selections to obtain data removal services here.
The mass security failure puts most popular browsers at risk in Mac
Kurt key takeway
Macreaper makes it clear that the most durable exploits are not zero days, but take moments of trust, an authentic -looking captcha, a useful solution, a clipboard that does what is told. As Apple tightens the technical screws with fast safety and notarly answers, wait for the adversaries to double into such psychological levers. Contra-strategy is to make healthy skepticism in user behavior and implement MACS with the same telemetry layers as companies already expect from Windows. Safety, in other words, has finally become an agnostic muscle of the platform, and complacency is the most risky operating system of all.
Do you think technological companies are doing enough to stop malware such as Macreaper? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter.
Ask Kurt a question or let us know what stories we would like to cover.
Follow Kurt in his social channels:
- YouTube
Answers to the most informed Cyberguys questions:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



