PayPal false email allow hackers to access the computer and bank account
Online scams are becoming more dangerous and convincing every day. Cybercriminals are finding new ways to obtain not only their login credentials, but also the total control of your computer and bank accounts.
Take John of King George, Virginia, for example. He recently shared his alarming experience with us. Its history is a powerful warning about the speed with which things can climb if it responds to suspicious emails.
This is what happened to John in his own words: “I answered by mistake a false email of PayPal that notified me of a purchase of the laptop. The message seemed real and I called the number listed. The person on the phone gave me a strange number to enter my browser, which installed an application that took control of my PC. A warning that appeared saying ‘software updating, not turning off, not turning off, not turning off, not turning off the PC, and I could see my full file system.
John’s fast thinking when closing his computer and alerting his bank helped minimize the damage. However, not everyone is so lucky.
Usa to the “Cyberguy Free Report: Obtain my expert technology advice, critical security alerts and exclusive offers, in addition to instant access to my Survival guide for the free final scam “ When you register!
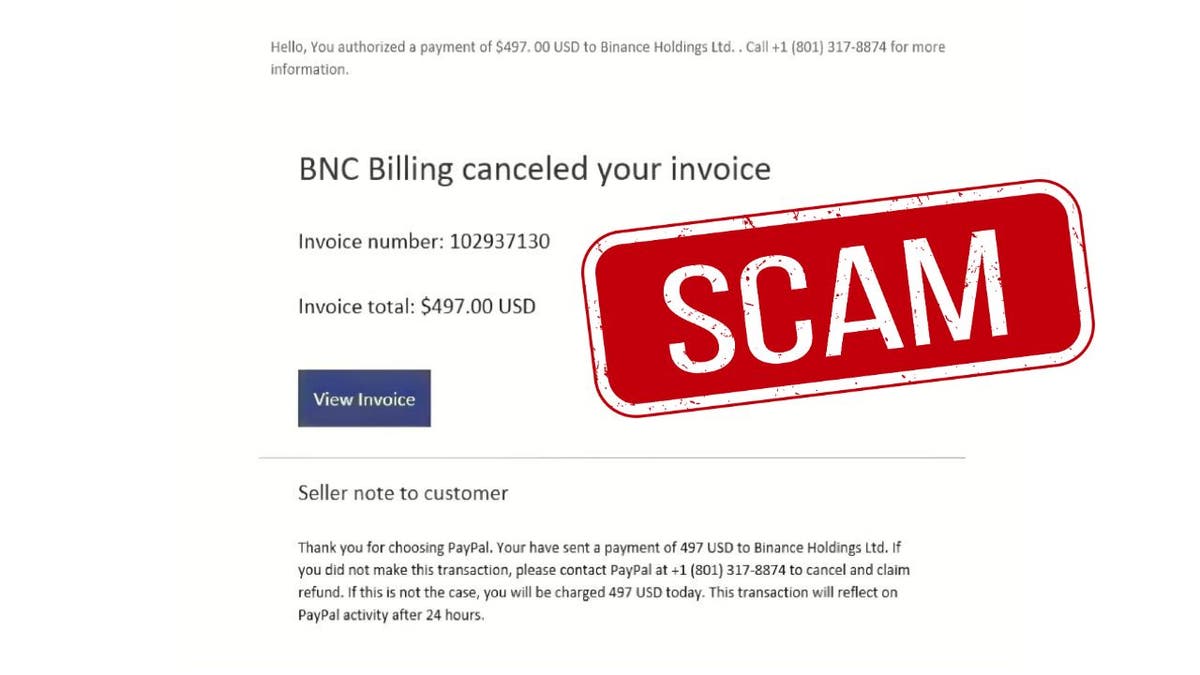
PayPal fake scam email (Kurt “Cyberguy” Knutsson)
How is this scam
This type of scam is known as a remote access scam. He often begins with a false email that seems to come from a trusted company like PayPal. The message states that there is a problem, as an unauthorized position, and urges the victim to call a phone number or click on a link.
What is artificial intelligence (AI)?
Once the scammer gets in touch, guides the victim to enter a code in his browser or install a program, claiming that he will solve the problem. Actually, this gives the scam the total control of the victim’s computer.
Once inside, scammers often look for confidential files, access the banking websites, steal login credentials or install malware to maintain long -term access. Even if the immediate scam stops, hidden malware can allow the scammers to enter the system later.

A hacker at work (Kurt “Cyberguy” Knutsson)
Urgent Paypal email scam that cannot be allowed to ignore
Takeways of John’s experience
John’s nearby call highlights several important lessons.
False emails are more difficult to detect than ever: The scammers create emails that are almost identical to the real of trusted companies like PayPal. They copy logos, format and even false customer service numbers. Always check the email address of the sender twice and verify the communications visiting the website or official application directly instead of clicking the links within the emails.
Remote access scams can climb quickly: Once the scammers get the control of their device, they can steal confidential data, move funds between the accounts and install hidden malware that is left behind even after the scammer disconnects. It often takes only minutes for serious damage to be done, which makes it critical of rapid recognition.
Psychological pressure plays an important role: Scammers trust to create a feeling of urgency and fear. By keeping it on the phone and urge the secret, they areolate it with help and hurry it to make bad decisions. Recognizing when pressed is key to breaking the control of the scammer.
Quick action can make all the difference: By quickly disconnecting his computer and contacting his bank, John limited the scam access to his accounts. Acting in a matter of minutes instead of hours can stop greater theft, block fraudulent transactions and protect your confidential information that they completely compromise.
Get the News business on the fly by clicking here

A warning on a laptop computer screen (Kurt “Cyberguy” Knutsson)
Do not click on that link! How to detect and prevent Phishing attacks on your entry tray
How to protect from remote access scams
Taking simple but strong security steps can protect it from being a victim.
1. never call a number that appears in a suspicious email: Scammers often configure false phone numbers that sound professionals, but are designed to handle it to deliver control or information. Always find verified contact information through the website or official application of a company, no links/numbers provided in suspicious messages.
2. Be an unusual instructions skeptic: No legitimate company will ask you to install software or enter foreign codes to protect your account. If something seems unusual, trust your instincts and stop communication immediately.
3. Install strong antivirus software on all devices: Antivirus programs can detect suspicious downloads, block remote access attempts and help prevent computer pirates from taking over their system. Having strong antivirus protection installed on all its devices is the best way to safeguard the malicious links that install malware and try to access their private information. This protection can also alert it to the PHISHING Electronic Correos and Ransomware scams, maintaining their personal information and their safe digital assets. Get my elections for the best antivirus protection winners 2025 for your Windows, Mac, Android and iOS devices.
4. Use identity theft protection: These services supervise financial accounts, credit reports and online activity for fraud signs, alerting it on suspicious transactions. See my advice and the best selections on how to protect yourself from identity theft.
5. React immediately if you suspect a scam: Disconnect your Internet device, communicate with your bank or credit card company immediately and change your passwords, especially for bank and email accounts. Monitor your accounts closely for unauthorized activity and report the scam to Federal Commission as well as the company that was supplanted. Acting can quickly avoid greater access and limit damage scammers that can cause.
6. Use multifactor authentication (MFA): MFA Add a critical safety layer beyond passwords, blocking the unauthorized session logger even if credentials are stolen. Enabling MFA in all accounts, especially banking, email and payment platforms, to prevent scams from avoiding stolen passwords.
7. Update devices and software immediately: Regular updates Patch Safety failures that scammers explode to install malware or kidnapping systems. Turn on automatic updates whenever possible to ensure that you are always protected against newly discovered vulnerabilities.
8. Use a password administrator with strong and unique passwords: Avoid password reuse and use complex password phrases to minimize credential fill attacks. A password administrator generates and stores unwavering passwords, eliminating the risk of weak or repeated credentials. Get more details about me The best password administrators reviewed by experts of 2025 here.
9. Never share access to the screen or the remote control concession: The scammers exploit screen exchange tools to steal passwords and manipulate real -time transactions. The legitimate technical support will never require undisputed screen access; Finish the call immediately if it is pressed.
10. Invest in personal data elimination services: These services automate requests to delete their personal information from data corridors and people search sites, reducing publicly available details scams could exploit for phishing or impersonation. While no service promises to eliminate all its Internet data, having an elimination service is excellent if you want to constantly monitor and automate the process of eliminating your information from hundreds of sites continuously for a longer period of time. See my best selections to obtain data removal services here.
Protect yourself from technical support scams
Kurt’s Key Takeways
John’s story is a reminder that online scams are quickly evolving and becoming more aggressive. Keeping skeptical, verifying all suspicious messages and acting quickly if something feels bad can make the difference between staying safe and losing confidential information. Protect your devices, trust your instincts and remember that it is always better to be cautious than risk with your safety.
Click here to get the News application
You or someone who knows has been the target of a scam like this? Get us knowing in Cyberguy.com/contact.
To obtain more technological tips and safety alerts, subscribe to my free Cyberguy Report newsletter when you head Cyberguy.com/newsletter.
Ask Kurt or tell us what stories you would like us to cover.
Follow Kurt in his social channels:
- YouTube
Answers to the most informed Cyberguys questions:
- What is the best way to protect your MAC devices, Windows, iPhone and Android to be pirate?
- What is the best way to stay private, safe and anonymous while navigating the web?
- How can I get rid of robocalls with data elimination applications and services?
- How do I eliminate my private internet data?
New Kurt:
- Try the new Cyberguy games (crosswords, words searches, trivia and more!)
- Cyberguy exclusive coupons and offers
Copyright 2025 Cyberguy.com. All rights reserved.
Kurt “Cyberguy” Knutsson is a award -winning technological journalist who has a deep love for technology, equipment and devices that improve life with their contributions for News & News Business Startzing Mornings in “News & Friends”. Do you have a technological question? Get the free Kurt’s free newsletter, share your voice, an idea of the story or comment on Cyberguy.com.



